Blog
ShareFile security threat alerts: what you need to know

We know how important security is to you and your clients. So, in addition to your regular employee security training, consider adding our security threat alerts to your workflows. These real-time alerts give employees a clear view into potential threats and actions they can take immediately after.
In this blog post, we’ll explain the value of empowering employees with tools to mitigate security risks and how to use this feature.
Empower employees with more security tools
As technology advances, so do the security risks. You can expand your security posture by equipping team members with more capabilities to detect and react to potential threats. Employees can take the necessary steps themselves or immediately notify the right channels. These alerts also prevent employees from having to loop in IT to understand basic threat information.
Build trust with clients through security
Security alerts show your clients that you have a proactive and transparent approach to safeguarding their data. This ensures that client data is protected, and any potential security threats are promptly addressed.
Clients receive alerts for activities related to their data and files, such as unusual access, failed sign-in attempts, or the presence of malware. These alerts make security feal personalized, and clients can take immediate action in response to security incidents.
For example, if a client receives an alert about unusual access to their files, they can report it or change their login credentials to mitigate potential risks. Or, if they receive alerts about failed sign-in attempts, they can be more cautious with their login credentials and take measures to strengthen their account security.
What are security threat alerts?
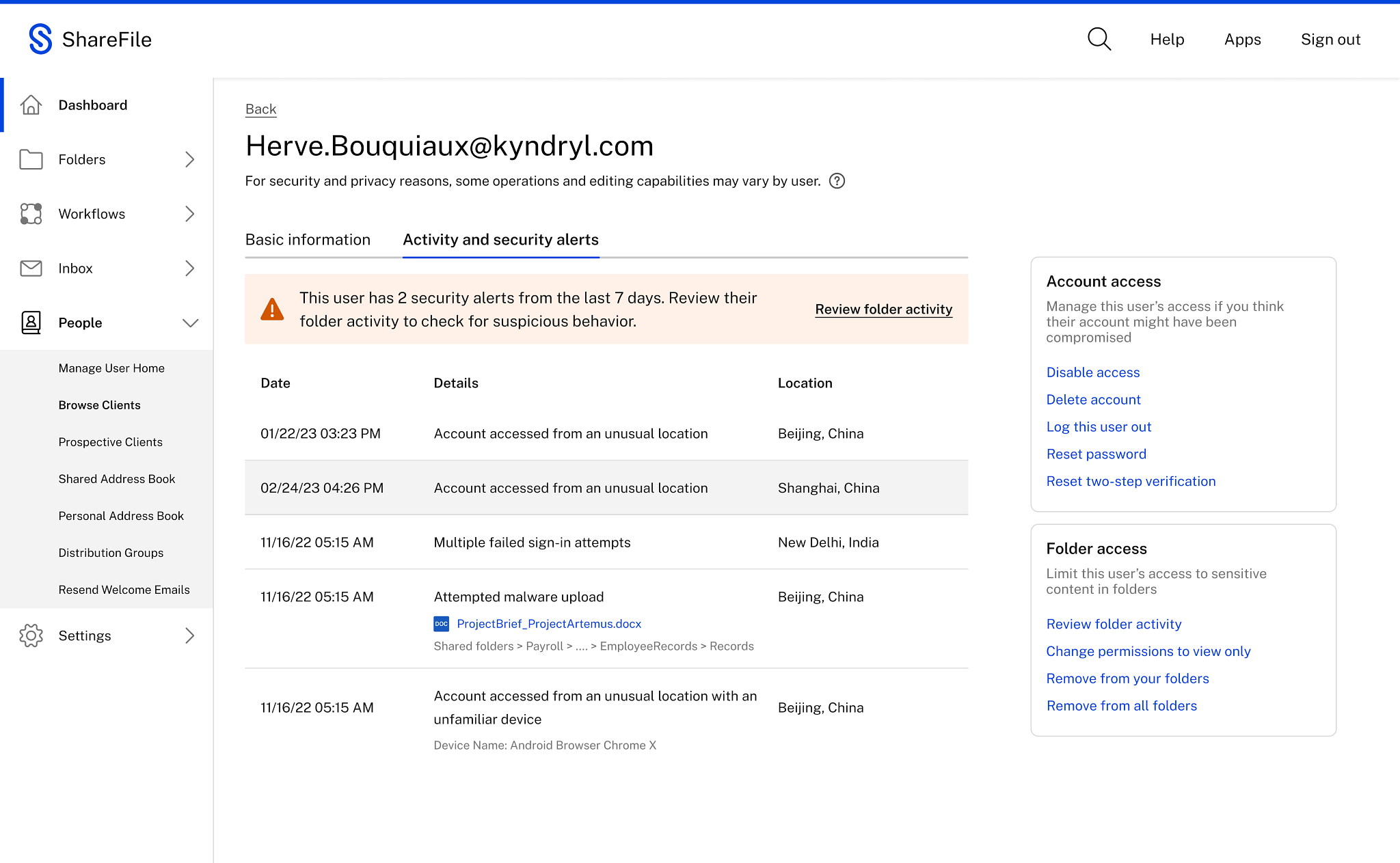
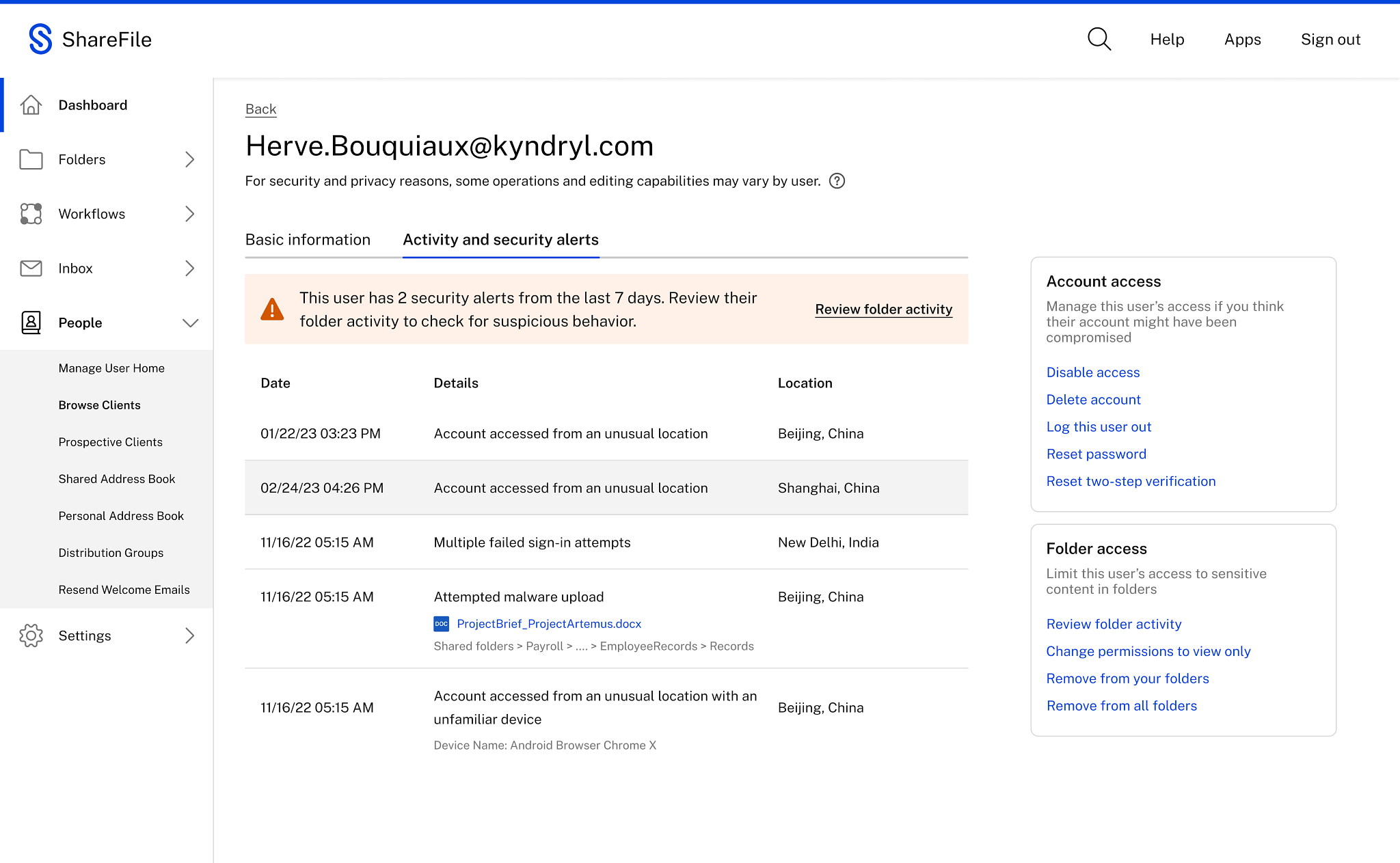
If ShareFile detects unusual account activity, it will send out an email alert so admins and employee users of ShareFile can act on threats as soon as they’re detected. Users have visibility into the threat context and history.
If the activity seems suspicious, from this same page, you can take soft actions such as signing them out or sending them a link to reset their password. Or you take harsher actions such as changing their access to view-only or removing their access from all folders you own.
What triggers an alert?
Our security threat alerts look out for some of the most common types of unusual activity. When alerted early, team members can take immediate action on these types of threats and potentially stop the issue from getting worse.
Malware upload
An alert is triggered when a file is uploaded to the system that may contain malicious software designed to harm or exploit a company device, network, or system. Examples of malware include viruses, spyware, and ransomware.
Suspicious location access
An alert is activated when an account is accessed from a location that's unusual or not recognized based on past usage patterns.
Unknown device access
An alert is triggered when an account is accessed from a device that hasn't been previously registered or recognized by the system.
Unusual authentication failures
An alert is triggered when there are multiple failed login attempts in a short period of time, indicating a possible unauthorized access attempt.
What information does the alert contain?
The alert provides a breakdown of the unusual behavior, covering specifics like the file and folder names, timestamps, and more.
Both ShareFile admins and folder owners, who will know their clients best, can delve into the user's recent login activity to identify anything out-of-the-ordinary.
To support quick and effective responses, the alert also offers next steps to mitigate potential risks. Some of the corrective steps include:
- Change password: If they receive an alert about unusual access or failed sign-in attempts, they can change their password to secure their account.
- Review files: If alerted about a malware upload, clients can review their files and delete if required. Admins can review, delete and quarantine the affected files.
- Employees: Employees can also take similar actions specific to their role and access permissions.
- Administrators: Administrators can take more comprehensive actions, such as blocking or suspending accounts, conducting investigations, or configuring security settings. Moreover, for a broader perspective on security metrics, users can access a comprehensive security alert dashboard.
How do administrators or employees take action?
A new security dashboard is accessed within the ShareFile web UI or directly from an email alert. The security dashboard serves as a central hub for comprehensive threat analysis and response. Within the security dashboard, administrators or employees will have access to detailed threat information, including the nature of the alert, a chronological timeline of events, files and folders details, and specific user and location details.
Who receives the alerts?
ShareFile admins and folder owners are the primary contacts responsible for folder content and security, and they receive immediate alerts via email. Admins have the power to tailor the alert settings for employees, choosing the specific threats they want to warn employees about.
Not only do the admins get alerted, but the system also notifies employee users that authored the potentially corrupt file or folder. This approach gives employees a clear view into content-centric risks, reinforcing a collective security mindset.
Even clients are alerted in real-time. This step reassures clients of your focus on protecting their privacy. Administrators on the account can control the alerts for their users.See the documentation page for more information on types of alerts sent per user.
Expand your security solution
Ready to get started with threat detection alerts? ShareFile Advanced and Premium customers have access to these new features and can take immediate action the next time an alert is sent.
Threat detection alerts are just one of many security layers we’ve added in 2023. We are taking steps to improve the security posture of file sharing. For example, users will see a new alert when they are about to share a link that can be viewed by anyone.
Also, we are making it easier for administrators to require authentication for all share or request links for the account. For more information, visit this article to learn about all of the new secure sharing options.
Related Resources

Blog